What exactly does the term RISK mean to you?
I attended a virtual conference recently that was focused on Third Party Risk.During the conference, participants talked about Risk, Continuous Monitoring and Assessment Management. Without fail the word “risk” came up numerous times and in multiple contexts. Inherent risk, residual risk, tiering methodologies, cyber security and third party risk. Mitigation of risk was a common theme. The terms high, critical, medium and the colors of red, yellow, and green were used across the board.
One presenter said “finding people who understand cyber risk is challenging.” Yet, it was clear that he himself did not understand what risk really meant. He consistently used the word risk, when threat would have been a more appropriate term. It was very clear that risk taxonomy in the third party risk management world is lagging when it comes to discussing risk in business terms.
Sitting through the conference reminded me of a blog that Nick Sanna, CEO of RiskLens posted in 2018 called What is Cyber Risk Quantification where he answers the question: What is ‘Cyber Risk’? from a standard risk taxonomy and risk quantification view of FAIR (Factor Analysis of Information Risk). I highly recommend reading the entire blog, but his short answer to that question is “According to FAIR, risk is defined as ”the probable frequency and probable magnitude of future loss” associated with a specific event. The way in which possible losses materialize must be articulated in risk scenarios that describe the action of a threat onto an asset of value and the resulting effect. In this picture, risk is synonymous with loss exposure.”
Nick also goes on to say that “…to accurately describe a risk scenario, one needs to define the asset of value, the threat, the threat effect and the resulting impact. If one of those elements are missing we can’t properly talk about risk.” Among conference participants, not a single vendor covered all of these components. Typically, they defined risk as some proprietary calculation they perform on their data-points, then display the risk as something in a range of numbers or letters, with a number basing the asset value on an inherent risk set of questions that ultimately resulted through their analysis in rankings such as high or critical. I tried to count the number of different risk definitions or phrases that were used, but lost track. One slide alone used the word “risk” more than 25 times.
Why terms matter
It is important that third party risk management professionals learn to speak about risk in the same language as it will allow them to focus their limited resources on vendors who present a high probability and/or impact risk beyond the organization’s risk appetite, instead of performing time consuming assessments on a vendor who poses a low probability of financial loss if an adverse event were to happen or on vendors who pose a little risk overall.
The common practice today is to tier vendors by inherent risk (usually defined as the risk present absent all controls). As Nick said in his article, “Customers and vendors alike use the term ‘risk’ liberally to describe things that sound scary and use it interchangeably to talk about threats, control deficiencies and forms of loss.” The use of this description for inherent risk is one of those uses whose purpose is to sound scary. Essentially, anything without controls would be “high risk” in this quantitative method.
Let me put this into the context of a popular TV show called M*A*S*H. MASH stands for Mobile Army Surgical Hospital. The purpose of the MASH was to be close to the front lines and treat wounded early, based on the severity of the wound (severity being directly related to the loss of life, early treatment being directly related to survivability). This type of tiering by criticality is called triage. I have heard some TPRM practitioners liken the tiering process to triage, but if we were in a MASH unit and tiered patients on a label, such as rank instead of injury, then it would be an epic failure with catastrophic loss of life and limb. The reason I say this is that the current TPRM tiering process is usually focused on qualitative terms like High, Medium, and Low, which has no viable connection to the probable frequency and probable magnitude of future loss.
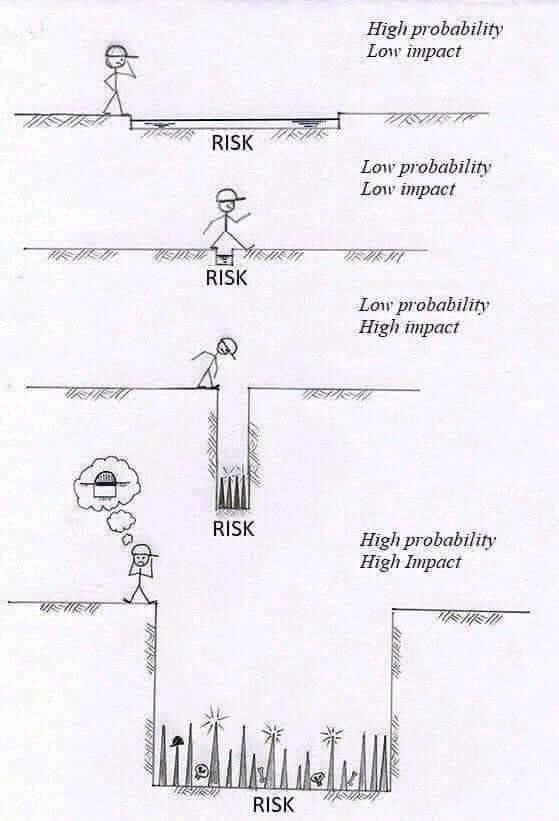
There is an image that I have seen circulated on LinkedIN that is a good start to helping to clearly explain the concept of risk. Comments on the image range from “Brilliant” to “Great illustration of the concepts of likelihood and impact.” I agree that it is a great image to clarify the understanding of risk, but it also adds to the confusion of what risk is.
The graphic conveys the idea of impact is the likelihood of an injury to the stick figure (I will call it the Sticky and it will be mine). The thought bubble of a bridge even introduces the idea of a mitigating control. Where the image fails is that it labels the threats at the bottom of the hole as the risk. Also, probability is left to the viewer’s interpretation. Is the Sticky an Olympic jumper who could easily clear the pits in all of the scenarios? Qualitative interpretation can make this image mean different things to different people, and that could spell disaster when you are presenting third party risk to the board or are experiencing a real-world risk-related failure.
Take a look and decide for yourself. What are your underlying thoughts about risk?
When you introduce reality into the cartoon, risk, as defined in FAIR, could be drastically different.
Questions about how often the Sticky traverses the path would be important, as well as his jumping ability or access to alternative solutions. The last pane, “high probability high impact” is essentially depicting common practice to define Inherent Risk. No controls (jumping ability, bridge) with the resultant impact being certain death is an impractical view of risk (the likelihood of death during a single traversal of the chasm).
Let’s look at the cartoon for the other scenarios. In reality, if we view third party risk in the same manner, this viewpoint provides no value for our program. The probability of death in the first three scenarios (for a single traversal) is low. Another factor that is missing in the cartoon is “why” the Sticky needs to cross the ditch in the first place or, stated another way, the value to the process. It is left to the viewers opinion and qualitative perspective.
Even at this level of analysis, we are still missing a key component of a valid risk assessment – what is the asset and what is the value? I believe everyone who views the cartoon assumes that the asset is Sticky’s health. The last pane of the cartoon shows skulls, so our assumption is skewed to think of death, but no where is the the value discussed. If it really were his health, then he simply does not need to cross the ditch at all.
So, what exactly does the term “risk” mean to you? As you build or enhance any risk management program that is a critical question you need to answer. One thing is certain, you cannot begin a conversation about risk without understanding what risk is, how it is defined, and how it shapes your company’s reality. Risk is the same for everyone, but risk tolerance is different for everyone.
The circumstances which shape your perception of risk may need updating. As you can see, defining risk can be a bit elusive, but it doesn’t have to be. Over three decades of risk experience in a variety of sectors I’ve seen risk in all types of organizations, and the FAIR model is by far the best for the current state of cybersecurity affairs at most companies.
Today, I see third party risk being treated in the same way as other risks were 20 years ago, using outdated approaches to new and evolving problems. The digital age has created access to so many things we never expected. It has increased our ability to be successful and enjoy the world. Yet, we are aware, now more than ever, of the downsides to this access. Data breaches are simply the result of exploiting the many vulnerabilities that exist in this digital environment.
Assessing the risk and its value is quickly becoming a critical need for many organizations. As you reflect on your own company’s supply chains, vendors, and interactions with other organizations, consider the value of these interactions. If there were a security breach or data loss, what would it cost and how can you mitigate it?
About Black Kite
Black Kite enables enterprises to assess, prioritize, and address the third-party cyber risk of any company, located anywhere, within 60 seconds. Using easy-to-understand scorecards, Black Kite not only provides standards-based letter grades on various risk categories along with data on how to mitigate each risk in priority order but also the first-ever automated tool to measure the potential financial loss caused by an attack on a supplier or partner. Black Kite provides the substance, scale, and speed needed to effectively assess and monitor the cyber risk posture of any company or organization.
Learn more at www.blackkite.com.